Sandeep Srivas
Privacy Coins, Secure Wallets, and Truly Anonymous Transactions: What Actually Works
May 12, 2025 in हिन्दी-उर्दू कविता
Half a dozen projects promise total anonymity. Most fall short. I’ve watched this space for years, and the mix of hype and real engineering can be frustrating. I’m biased, but privacy that’s bolted on rarely holds up under scrutiny. The coins built from the ground up for privacy—where privacy is the default—behave differently. That distinction matters if you care about more than plausible deniability; it matters if you need protections that survive real-world scrutiny.
Okay, so check this out—there are two separate problems people confuse: the cryptography that makes transactions private, and the operational security (OpSec) that keeps your identity from leaking. Both must work. One can’t fully compensate for the other. You can use a privacy coin with the best cryptography and still leak your identity through sloppy wallet use, reused addresses, or obvious timing patterns.
First impressions: Monero gets the most attention for a reason. Its ring signatures, stealth addresses, and RingCT provide on-chain obfuscation that holds up better than simple mixers or “privacy modes” bolted onto transparent chains. That said, nothing is magic. My instinct said “this is strong,” but then I dug into how real users screw it up—exchange KYC, careless metadata, or linking blockchain activity to off-chain identities. So yes, the tech is solid; the ecosystem is the weak link.

Why architecture matters (and why a wallet is more than an app)
On one hand, a privacy coin must hide sender, receiver, and amount; on the other hand, the wallet must avoid leaking metadata through network traffic, update channels, or UI prompts. If a wallet phones home to a third-party server for balance checks, your anonymity evaporates—quickly. On the other hand, using a wallet that runs everything locally (or connects to trusted remote nodes over encrypted channels) preserves much of what the coin gives you.
Here’s what bugs me: many guides treat the wallet like a convenience. It’s not. It’s the user’s privacy boundary. Use an audited, open-source wallet. Verify binary signatures when possible. Prefer wallets that let you run your own node, or that connect to known, trusted remote nodes via encrypted connections. If you’re just getting started, a reputable monero wallet is where many privacy-focused people begin—because it integrates with privacy-aware node options and supports the coin’s native privacy features without unnecessary extras.
Seriously, check software provenance every time you update. Updates give attackers opportunities. A small inconvenience—verifying release signatures—can save you from a catastrophic leak. I’m not trying to be alarmist; it’s just how things fail in the wild.
Wallet types: tradeoffs you should know
Hardware wallets: excellent for securing keys offline. They reduce attack surface for key extraction and are a solid choice for holding larger amounts. However, hardware alone doesn’t hide transaction metadata; you still need to consider the node you connect to and how transactions are broadcast.
Light wallets: convenient, but they typically rely on third-party servers to query balances. That centralization can leak info. Some light wallets mitigate this by using encrypted, privacy-preserving relays or by connecting to remote nodes over Tor. If you must use a light wallet, pick one with clear privacy tradeoffs and configurable network settings.
Full-node wallets: the gold standard for privacy. Running your own node means you don’t trust a third party with address queries or transaction propagation. It’s heavier on resources, but it keeps your metadata tight. For many privacy-minded users in the US, running a node on a low-cost VPS or a small home server behind Tor is the sweet spot.
Operational privacy: the parts people skip
OpSec is where most failures happen. Use cases shape risk: casual privacy-seeking users have different needs from activists, journalists, or businesses. A few practical rules that actually help:
- Segregate wallets for different purposes. Don’t mix funds for high-risk and low-risk activity.
- Minimize address reuse. Stealth addresses are great—use them.
- Use Tor or a VPN that you control for wallet traffic; prefer Tor to reduce correlation via ISP logs.
- Avoid linking KYC exchanges to your privacy wallet. If you must cash out, consider privacy-respecting rails and accept the legal risks in your jurisdiction.
- Keep software current, but validate releases. Seriously—validate signatures.
One caveat: some tactics used to “increase privacy” can backfire legally. I’m not a lawyer. If your operations cross lines in your country, that introduces different risks. I’m not giving legal advice—just pointing out practical hazards.
Usability vs. privacy: the eternal compromise
Privacy tools often feel clunky. That’s partly a design problem and partly a trust problem: seeing fewer convenience features reduces the attack surface, but it also raises adoption barriers. Wallet designers face hard choices: add cloud backups (convenient, risky) or force manual seed storage (safer, more annoying). There’s no free lunch. Decide what level of friction you can tolerate and design your setup around that.
Personally, I accept a little extra friction for stronger guarantees. Others won’t. That’s fine. The key is to make an informed tradeoff, not one based on marketing or a catchy UI.
FAQ
Are privacy coins legal in the US?
Mostly yes. Owning and transacting with privacy-oriented coins is legal in many places, including the US, though regulators watch them closely. The legality can change depending on how you use them—especially if they’re used to evade sanctions or launder money. Follow local laws and consult counsel if you’re handling significant sums or operating a service.
How private is Monero compared to other coins?
Monero’s default privacy features (stealth addresses, ring signatures, RingCT) are robust for on-chain privacy. Unlike add-on mixers, Monero’s privacy is baked into the protocol, which makes it more consistent. That said, off-chain behaviors—exchanges, metadata leaks, timing analysis—still affect overall privacy.
What’s the safest wallet setup for strong privacy?
Run a full-node wallet locally or connect via Tor to a trusted remote node. Use hardware wallets for key custody, verify all software signatures, and maintain disciplined OpSec (no address reuse, separate wallets, cautious exchange interactions). There’s no single perfect setup, but these practices together reduce risk substantially.
Why a Contactless Smart-Card Might Be the Best Cold Storage You’ve Never Tried
May 7, 2025 in हिन्दी-उर्दू कविता
Whoa! Okay, so check this out—I’ve been fiddling with cold storage devices for years. My instinct said hardware wallets would stay king, but somethin’ felt off about clunky keycards and seed phrases everywhere. Really? Yes. There’s this quieter category—contactless smart-card wallets—that quietly solves a bunch of UX and security problems at once, and folks looking for a tidy, real-world solution should pay attention.
Short version: a smart-card that holds keys offline and communicates by NFC gives a user-friendly feel without throwing away security. Medium sentence for the win. Long sentence now—thinking about real world usage, where people pay, commute, and check prices on their phones, it makes sense to have a storage device that feels familiar (like a credit card), is hard to hack remotely, and still plays nicely with mobile apps, though of course trade-offs exist.
Let me be honest—I’m biased toward tools that reduce human error. That bugs me the most: people lose coins not because of exotic attacks but because of bad ergonomics. On one hand, seed phrases are robust and well-understood; on the other hand, they are fragile in practice because humans mis-handle them, mis-store them, or mis-type them. Initially I thought the seed model was untouchable, but then I started seeing people treat metal plates and paper backups like bricks—rarely retrieved until it’s too late. Actually, wait—let me rephrase that: seeds are sound in theory; in practice they’re often a usability liability.
Here’s a quick story—no fluff. I once watched a friend nearly trash a laminated backup because she thought it was trash. Seriously? Yep. That day convinced me the interface matters more than we admit. So I began testing alternatives: multisigs, Shamir backups, and a range of hardware wallets that read like sci-fi cards. The smart-card approach kept coming back as the pragmatic winner for everyday users who want cold storage but also want simplicity.

How contactless cold storage actually changes the game
Think of cold storage and picture a bank vault. Now picture a tiny vault you can slide into your wallet. That shift in metaphor helps—because comfort and frequency of use drive behavior. Contactless smart-cards remove the need to copy long seeds by hand, and they can use secure elements (the same tech banks use) to store private keys in a way that keys never leave the card. On the surface that sounds simple, but the practical upshot is big: fewer steps, fewer mistakes, less mental overhead.
Let me clarify—I’m not saying it’s flawless. NFC exchanges can be intercepted if your phone is compromised, and a lost card is still a physical risk. On the flip side, these cards can be PIN-protected, require physical contact to sign transactions, and some implement a seedless model where the card itself generates and safeguards the key without exposing a mnemonic at all, which reduces human-handling risk dramatically.
Okay, so check this out—I’ve been using one of these cards in daily testing. It’s delightfully low-friction. When I want to sign a transaction, I tap my phone to the card, approve with a short PIN, and the signature happens. No seeds on paper. No typing. No cloud. It feels like contactless payments, which people already trust. I’m biased, but that UX is crucial, especially for newcomers who find seed words intimidating.
Security-wise, the architecture matters. Good smart-cards use certified secure elements that resist physical tampering and side-channel attacks. They also minimize attack surface by limiting interactions to signing requests only. That said, adversaries adapt—so layered protections are key: PINs, transaction confirmation screens, app-level checks, and safes or RFID-blocking sleeves when carrying the card. I’m not 100% sure any single measure is enough alone, but combined they offer strong practical protection.
Here’s what bugs me about older models: too many devices assume people will do a perfect backup ritual. They rely on abstract trust that real humans rarely show. With contactless cards, the philosophy flips—protect the key where it is, and make recovery straightforward without waving a seed phrase at the world. There are trade-offs in flexibility, though. For example, if you want to derive dozens of accounts deterministically and manage them externally, some card models are less flexible than seed-based wallets. On the other hand, many users only need a handful of addresses and prioritize safety and convenience.
So where does tangem fit into all this? I forced a lot of real-world tests and returned to a few commercially mature options that strike the right balance between security and usability—one of which is tangem. Their cards implement a seedless model with secure elements, enable contactless signing, and keep the user flow minimal—tap, enter PIN, approve. No mnemonic to copy, which for many people removes the biggest point of failure. It isn’t perfect for every advanced use case, but for everyday cold storage and contactless signing it’s a compelling pick.
Alright, a little technical nuance—hold up. Contactless doesn’t mean online. The card never needs to be connected to the internet; it only communicates short-range with your mobile device. The phone is just a messenger. That limited communication is both its strength and its weakness: if your phone is compromised it can push malicious signing requests, but with a good app showing transaction payloads for human review and with conservative defaults, the risk can be controlled. On one hand, human review isn’t flawless; though actually, visual confirmation drastically raises the bar for attackers compared to blind keyboard-based signing.
One more tangent (and I promise it’s useful): think about travel. I once traveled with a hardware wallet and my backup seed in the same bag—dumb, I know. If that bag was lost, everything was gone. With a smart-card approach, you can split devices: card in secure place, backup card somewhere else, or use a metal plate for a redundancy copy. The card’s form factor makes it easier to separate holdings physically—put one card in a hotel safe, another in your pocket. This practical flexibility reduces single points of failure.
Users often ask me: what about multisig? Good question. Multisig remains the gold standard for losses and custodial risk, but it’s more complex to set up and use. Contactless cards can fit into multisig schemes, though support varies by wallet ecosystem. For many individuals, a single smart-card with strong physical protections and clear backup policy is a huge step up from insecure custodial exchanges or messy seed handling.
Let’s talk threats fast. The major risks are: lost/stolen cards, phone compromise, physical tampering (if the adversary has time and tools), and supply-chain attacks. Mitigations? PINs, tamper-evident packaging, buying from trusted vendors, and verifying card firmware/attestation when possible. Also, keep the card’s serial and identifying data private—don’t plaster it online. These are basic hygiene steps, but people forget them. I’m human; I forget too… sometimes.
Practical checklist for someone choosing a contactless smart-card:
– Confirm the card uses a certified secure element. Medium sentence to explain briefly. Long sentence: check for formal certifications or well-documented attestation mechanisms because those details reveal the card’s resistance to cloning and tampering, which matters if you value long-term holdings and plan to keep funds offline for years.
– Prefer seedless or non-exportable private keys if you dislike managing mnemonics. This reduces human error. But accept it may limit advanced recovery options.
– Use a PIN and enable anti-brute-force lockout. Simple, but very effective.
– Store a physical backup strategy: metal plate, second card, or secured deposit box—however you sleep better at night. I’m biased toward splitting copies.
– Keep your card firmware and companion app updated, and buy from reputable channels. No shady marketplaces. Really, don’t cut corners here.
FAQ
Is a contactless card as secure as a traditional hardware wallet?
Short answer: often yes, for typical users. Medium answer: many contactless cards use the same secure elements as traditional hardware devices, making the core key storage extremely robust. Long answer: security depends on implementation, app UX, and user behavior—so vet certifications, app reviews, and your backup plan before trusting large sums.
What happens if I lose the card?
Immediate steps: treat it like a lost credit card—move funds if possible and use backups. If you followed best practices (split backups, secondary devices), recovery is straightforward. If you didn’t—well, that’s the risk. I’m not sugarcoating it.
Can these cards be used for contactless payments too?
Some cards are designed purely for crypto signing and not for NFC payments. Others integrate payment rails. Know your model. If you want both functions, verify specs and security trade-offs—combining features sometimes expands the attack surface.
Wrap-up thought—I’m calmer about recommending smart-card cold storage than I used to be. There’s a real human advantage: less friction, fewer mistakes, and a model that maps directly to familiar behaviors like tapping and signing. That doesn’t mean toss your multisigs or your steel backups. It means consider a contactless card as part of a modern, layered defense: practical, portable, and painfully user-friendly—which, in crypto, is half the battle. Hmm… I still worry about supply-chain attacks and about users skipping basic hygiene, but overall, this tech is a welcome step toward real-world crypto security that people will actually use.
How I Learned to Stop Worrying and Trust the Simulation: dApp Integration with rabby wallet
May 4, 2025 in हिन्दी-उर्दू कविता
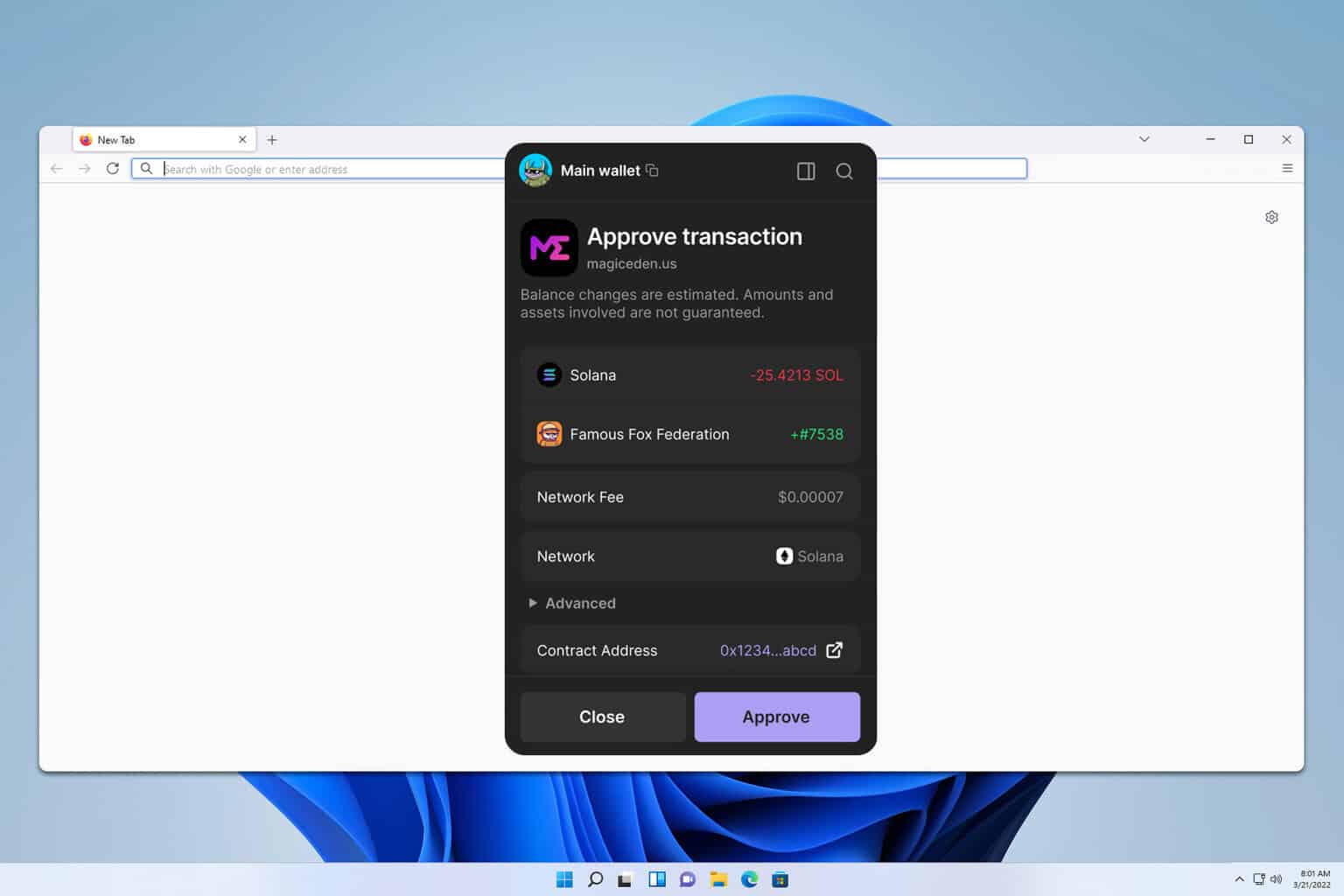
Whoa! The first time I saw a transaction simulation pop up in my wallet, I felt oddly relieved. My instinct said: finally, a sanity check before that “confirm” button nukes my balance. Initially I thought this was just marketing fluff, but then I watched a pending swap estimate gas at twice the quoted amount and that changed everything. Actually, wait—let me rephrase that: seeing a dry run save me from a bad approval pattern made me rethink how I build dApp UX.
Seriously? Yes. Smart contract interactions are messy. There are approvals, delegate calls, multicall bundles, and opaque mempool activity that can make even experienced users blink. On one hand, UX often glosses over these; on the other, wallets can expose too much raw data and scare users away. So the practical middle ground is simulation plus clear explainers—simulate first, then speak plainly.
Okay, so check this out—when a dApp integrates with a wallet that simulates transactions, two things happen. Bad flows get caught early. Good flows get optimized for gas and nonce order. My gut said this would be enough, but somethin’ else matters: how the wallet surfaces the simulation results. A tiny icon or cryptic log won’t cut it for everyday users.
Here’s what bugs me about common integrations. dApps often assume the wallet is a dumb signer. Though actually, modern wallets can do a lot more: they can predict reverts, flag dangerous approvals, and even suggest gas tweaks. On top of that, wallets that support EIP-712 signing or contextual metadata allow dApps to present intentions clearly, which reduces phishing and UX friction.
Hmm… there’s also the developer side. If you’re a dApp dev, you want deterministic sims. You want to reproduce a user’s failure locally before you push them to mainnet. That means using the same chain-state and node behavior, running eth_call with the final block, and accounting for pending mempool txs when appropriate. It’s subtle, but these details decide whether your on-chain simulation matches reality.
Working through contradictions: I used to think heavy-handed permission models (like infinite approvals) were just efficiency hacks. Now I see them as attack surface multipliers. On one hand, granting broad allowance reduces friction; on the other hand, it’s a persistent vulnerability if a contract gets compromised. So the safer pattern is scoped allowances and queued permissions—approve per-action or use a permit pattern when possible.
One practical pattern I keep recommending is: show a single-sentence intent, then the sim output, then an actionable choice. For example—”You’re about to swap 1 ETH for 3,200 USDC. Estimated gas: 0.004 ETH. Likely to succeed.” Then offer “simulate again” and “proceed” options. That small step increases user trust fast. It’s low friction and surprisingly effective.
Oh, and by the way, don’t forget replay and front-running risks. Simulations should include checks for slippage protection and sandwich vulnerability indicators when possible. Some services will annotate whether your trade is likely to be picked up by bots. If your wallet can surface that, users will thank you—loudly.
Now, about the nuts-and-bolts of integrating a wallet like rabby wallet into your dApp ecosystem: think in terms of capabilities, not just RPC calls. Rabby offers a UI focused on transaction clarity and security, and can act as a simulator that gives users a readable breakdown before signing. Design your dApp to request that breakdown and parse it into plain-English statements for the user.
Implementation tip: use eth_estimateGas and eth_call for dry runs, but also include a local state snapshot when possible. Create a test harness that replays edge cases—nonce wars, reverts from dependent contracts, and gas spikes. I learned this the hard way when a mainnet fork caused a previously stable bundle to fail—very very embarrassing. Testing with real-world noisy mempool conditions saves headaches.
On permission models—consider EIP-2612 permits where feasible. They let users sign intent off-chain to reduce approvals and gas. Initially I thought every dApp needed permits, but then I ran into contracts that didn’t implement them, so now I design fallbacks. It’s pragmatic: try permit, else fall back to minimal scoped approvals with clear expiration or revocation paths.
Security features to bake into your UX: show the contract address with ENS/contract verification; display a short plain-language summary of what the contract call will do; highlight value transfers and token approvals; and surface a simulation’s revert reason when available. If the wallet gives a line-by-line opcode or event trace, translate the key points into digestible bullets for users who aren’t devs.
Yeah, sometimes I ramble. But there are other concrete checks—nonce handling, gas limit buffers, and bundling multi-call sequences atomically. If your dApp does a batch operation, simulate the entire batch as a single transaction; if one call reverts, the user must know which one and why. This prevents partial-state surprises and ugly rollbacks.

Contract Interaction Best Practices
Start with clarity. Label every action. Offer a “Why am I signing this?” explainer. Then provide simulation results and a suggested gas strategy based on historical blocks. I’m biased, but transparency reduces support tickets and user churn—it’s measurable. For deeper safety, add a “watch mode” that alerts users when their allowance changes or when a token withdraw happens unexpectedly.
Developer ergonomics matter too. Expose hooks that let your front-end request a simulation and receive a structured response (success probability, estimated gas, revert reasons, and signature metadata). If the wallet supports contextual signatures (EIP-712), use that to attach intent and human-readable payloads. It creates better audit trails.
FAQ
How accurate are simulations?
Simulations are increasingly reliable, but not perfect. They depend on node state, pending txs, and exact gas dynamics. Use them as strong indicators, not absolute guarantees, and always show uncertainty ranges to users.
Can a wallet simulation prevent MEV attacks?
Not entirely. Simulations can flag high-risk trades and suggest mitigations (slippage tightness, gas boosts, or delayed execution), but they can’t fully stop bots unless paired with execution services that protect against front-running.
What’s the fastest win for dApp teams?
Add a readable simulation step before any high-value approval or transfer. It costs little development time and yields outsized trust gains—users feel safer, and you get fewer support calls. Seriously, it’s that effective.
Why Decentralized Perpetuals Feel Different — And How to Trade Them Smart
April 30, 2025 in हिन्दी-उर्दू कविता
Okay, so check this out—decentralized perpetuals are finally getting interesting. Wow! They look like centralized futures at a glance, but the mechanics are often very different. My instinct said “this is easy,” but then I watched a funding cycle and changed my mind. Initially I thought blockchains would just replicate exchanges; actually, wait—let me rephrase that: the tech copies features, but the economics and UX diverge in ways that matter.
Here’s what bugs me about a lot of coverage: people treat “perpetuals” as if they were a single product. They’re not. Some are AMM-driven. Some use order books. Some mix on-chain settlement with off-chain order matching. Those design choices change everything—from slippage to liquidation paths to who eats your fees. Really?
Short version first. Perpetuals let you hold leveraged exposure without expiry. They use funding to tether price to an index. But the devil is in the parameters. Long funding favors shorts. Short funding favors longs. And if you ignore that, you will get eaten alive by compounding. Hmm…
Let’s slow down and walk through the lived realities. On one hand, decentralized perpetuals can be more transparent. On the other hand, transparency introduces new attack surfaces. I’ll be honest: I trade them; I feel the friction. Sometimes somethin’ seems oddly slow. Trading on-chain gives you provenance. But it also bumps you up against gas, oracle cadence, and sudden liquidity disconnects.
Funding rates are the heartbeat. If longs pay shorts, that funding flow will slowly bleed levered bulls. If you hold one-sided exposure for several funding periods, the cost compounds. My gut told me to ignore small funding, though actually compounding made a mess of a position I held overnight.
Liquidity, Slippage, and Execution Reality
Liquidity in a DEX is not just depth. It’s also how that depth is routed and how concentrated it is. So, slippage feels different because liquidity can be fragmented across pools and epochs. In AMM-based perps, your execution price depends on virtual inventories and funding oracles. In order-book hybrids, your fill depends on relayers and matching engines that sometimes prioritize size over fairness.
On-chain settlement removes counterparty risk. It also exposes you to oracle latency. If an oracle lags during a flash crash, liquidations can cascade wrongly. That’s why reading the whitepaper matters—but also why watching the mempool and oracles in real time matters. Seriously?
Risk management isn’t theory. It’s timing. Your stop orders might never execute at the expected price when gas surges. So you need contingency plans: smaller sized entries, staggered exits, and an eye on funding drift. On one hand, leverage multiplies gains. On the other hand, it magnifies microstructure issues that centralized venues absorb or hide.
Here’s a practical checklist I use. First, check the funding window cadence. Second, estimate expected slippage for your size. Third, precompute liquidation thresholds under different oracle feeds. Fourth, size positions so that a couple of funding periods don’t bankrupt you. That sounds basic, but it solves a ton of surprises.
Perps Design Patterns and What They Mean For Traders
There are three dominant patterns you’ll see. Pattern one: AMM perps with virtual inventories. Pattern two: perpetuals with order-books and on-chain settlement. Pattern three: hybrid systems that rely on off-chain matching plus on-chain clearing. Each brings tradeoffs.
AMM perps are predictable in cost curves, and they are permissionless. However, they can have heavy slippage for large trades, and they often implement funding with a clear feedback loop. Order-book based perps can offer better fills for size, though they sometimes centralize matching and reintroduce counterparty cleavage. Hybrids try to balance both, but they add coordination complexity which can produce edge cases.
Initially I favored AMM perps for simplicity, but then I realized order flow matters. Liquidity providers behave differently on-chain. They hedge with on- and off-chain positions, and sometimes they pull liquidity into venues that reproduce better spreads. On the whole, that behavior can cause erratic effective spreads.
One more thought: insurance pools and socialized losses. Some protocols absorb small liquidation deficits via insurance, others pass them to LPs, and some use auto-deleveraging. Know the rules. If you think your liquidation will be handled “fairly,” you’re probably wrong—so read the mechanism docs.
Leverage Strategies That Actually Work
Don’t treat leverage as a multiplier of confidence. Treat it as a multiplier of uncertainty. Small leverage, sized for buffers, usually wins over time. A lot of traders chase 10x or more because it looks sexy. But volatility and funding compound costs kill more positions than market direction.
One practical tactic is dynamic sizing. Start with low exposure, add into conviction bands, and reduce before expected volatility events. Another is cross-margin prudence. Cross-margin ties your accounts together; it reduces forced liquidations on small moves but increases tail risk across your portfolio. Is it worth it? Sometimes, though I’m biased toward isolated margin for smaller accounts.
Take hedging seriously. If you run a leveraged long, consider a short-dated hedge or options overlay where available. Hedging reduces the reactivity of liquidations and gives you breathing room during funding swings. Also—this is key—factor in funding direction when structuring hedge windows.
Oracles, MEV, and Attacks — Not Just Theory
Oracles are the pulse that ties on-chain prices to external markets. If the pulse is noisy, your trade can flail. I’ve seen oracles misprice for a few blocks and trigger mass liquidations. Those moments are ugly. On the bright side, proper oracle design—medianized prices, multiple feeds—reduces risk.
Then there’s MEV. Miners or validators can reorder transactions, extract funding arbitrage, or sandwich trades. You can’t ignore that. Use private relays or gas strategies when executing sizable orders. Also, watch for funding “games” where market participants push indices to extract payments via funding arbitrage.
On one hand, decentralization removes a single point of failure. On the other, it introduces local incentives that can be manipulated. So know the incentives and adapt your execution accordingly. This is something that trips up new traders who assume “decentralized” equals “neutral.”
Where to Trade — Practical Recommendation
If you want to sample a well-architected DEX with perpetuals, try a platform that balances liquidity, oracle resilience, and transparent funding mechanics. Check latency, check how liquidations are socialized, and test small. One practical landing spot is hyperliquid dex, which attempts to marry deep liquidity with clear funding math. I’m not endorsing blindly. But it’s worth a look if you favor transparent AMM design with better routing.
Do a dry run with minimal leverage. Watch the funding over several cycles. See how any liquidation events were handled historically. If their docs are terse or their UI hides funding history, that’s a red flag. (oh, and by the way…) keep an eye on their governance mechanisms too; that tells you who bears future protocol risk.
Quick FAQ
How much leverage is safe?
There is no universal safe leverage. For most retail traders, 2x–3x with tight risk rules is reasonable. Higher leverage demands advanced monitoring, quick execution, and contingency capital. Remember funding costs compound and can flip profits into losses over time.
What causes unexpected liquidations?
Oracle glitches, sudden funding spikes, fragmented liquidity, and mempool MEV. Also, simple human mistakes—overleveraging, ignoring upcoming data releases, or mistyping orders. Be humble; assume errors will happen and plan accordingly.
Are on-chain perps better than centralized ones?
It depends. On-chain perps offer transparency and censorship resistance. Centralized perps often provide tighter execution and lower latency. Choose based on what you value most: decentralization and composability, or low slippage and familiarity.
Closing thought: decentralized perpetuals are a new frontier with familiar traps. They’re exciting, but they force you to think differently about liquidity, funding, and settlement. I like them, yet parts of the space still bug me. If you approach them with curiosity and conservatism, you’ll learn fast. If you rush in for edge, you might learn faster—and lose faster too. Trade smart, watch the funding, and keep a margin buffer. Somethin’ tells me that the best opportunities will go to the traders who respect both on-chain mechanics and old-school risk rules.
Why logging into your Coinbase account shouldn’t feel like a panic attack
April 27, 2025 in हिन्दी-उर्दू कविता
Whoa! Logging into your Coinbase account can sometimes feel like a rite of passage for new crypto traders. Really, between 2FA prompts, device checks, and those mysterious email confirmations, it gets messy fast. Initially I thought it was just poor UX, but then I realized a lot of the friction is intentional—it’s protecting millions of dollars and preventing fraud, even if it drives you a little nuts. Here’s the thing: with a few habits and a couple of practical checks you can speed up access while keeping security tight.
Start simple: use the official Coinbase app or the verified website, and bookmark it in your browser. Don’t click links in random emails; that one rule alone stops a lot of problems. Seriously? Yup. If you get locked out because of failed attempts or location changes, Coinbase’s security engine will flag the session, which is good for safety but bad for your nerves when you need to trade quickly. So keep a recovery email that’s current and a phone number you actually pick up.
Wow! Two-factor authentication is just non-negotiable for me as a trader. SMS works, but an authenticator app or a hardware key is far safer. My instinct said hardware keys were overkill, but after watching a colleague’s account get phone-SIM swapped, I switched to a YubiKey and slept much better—no kidding. If you use an authenticator app, backup your codes or store the seed securely offline. And yes, write it down somewhere physical—don’t trust cloud notes for this.
Privacy-conscious browsers and extensions can sometimes interfere with Coinbase’s login checks. Hmm… On one hand I want privacy protections, though actually some ad blockers or anti-fingerprint extensions block the scripts Coinbase uses to verify devices, and that can trigger additional verification steps and delays when you try to log in from a trusted machine. So either whitelist Coinbase or set aside a clean browser profile for exchanges and finance sites. It sounds annoying, but it’s a practical trade-off between convenience and fewer false locks.
The mobile app has push notifications that streamline approvals for new device sign-ins. Really? Yes—push is usually faster than SMS and less vulnerable to SIM attacks. When push approvals act oddly—like requests appearing without your intent—treat them as a red flag; revoke sessions, change your password, and contact support because someone may have your credentials or have initiated a session on your behalf. Enable biometric unlock if your phone supports it; it’s faster and still strong. And keep your phone’s OS updated; old versions have vulnerabilities that make account takeovers easier.
If you lose access, Coinbase’s recovery flow asks for identity verification and proofs—be ready with scans. I’m biased, but having clear photos of your ID and a steady internet connection shaves hours off the wait. Initially I thought automated recovery would be seamless, but actually, wait—let me rephrase that: it’s thorough and sometimes slow, and patience (plus clear photos of your ID and a steady Wi‑Fi connection) makes the process move faster. If you’re in a hurry, document everything and start recovery early. Also, store recovery phrases for wallets in a physical place—digital backups can be hacked or accidentally synced away.
Tighten account settings: enable alerts for logins, review connected apps, and periodically check active sessions. Here’s the thing. Phishing emails are crafty—check the sender, hover over links, and watch for misspellings (those tiny tweaks are a favorite trick). On the other hand, sometimes legit emails get messy or routed through different mail servers, so when in doubt log in directly through your bookmarked site rather than via the message, and if an email pressures you for immediate action that’s often a red flag. Use separate passwords for your exchange account and email; don’t reuse credentials.
For active traders, session timeouts and verification delays cost opportunities. Whoa! So plan ahead: if you expect to trade during high volatility, make sure your 2FA is working, your balance is visible, and your withdrawal whitelist (if used) will permit quick movements, because during pauses you might miss a window. Also, set price alerts and use limit orders to reduce frantic logins during pumps. Practice a preflight routine—open the app, confirm balances, set orders; this avoids fumbling when markets move.
Common issues include outdated app versions, time-sync problems on your device, and cached cookies. Hmm… If a code doesn’t arrive, check spam, network connectivity, and your phone’s Do Not Disturb or message filtering. If push notifications stop, try removing the device from Coinbase sessions and re-adding it; sometimes a clean re-login with app updates and cleared cache resolves the issue—annoying, yes, but effective. Don’t try shady browser extensions or random “login helpers”—they often introduce malware. And if something smells phishy, trust your gut—somethin’ is often off.
Coinbase is regulated and conducts KYC, which many traders grumble about but that’s the reality. I’m not 100% sure, but regulation is part of why exchanges can offer USD fiat rails and debit/credit integrations in the US. On one hand KYC means less privacy than self-custody, though actually it also means your account has recourse if compromised, and that trade-off matters depending on whether you prioritize anonymity or recoverability. If privacy concerns you, segregate funds: trading balances on exchanges, long-term in cold wallets. That approach gives you agility plus added security benefits.
Quick pointer
Okay, so check this out—For official help or to double-check login procedures, use Coinbase’s verified pages. If you need step-by-step login instructions or recovery options, try the guide at coinbase. My experience is that reading the official walkthrough before you panic saves time, because support queues get long during market swings and having your details ready speeds up verification. And remember: the site will never ask for your full password via email or social media.
I’ll be honest: some of this stuff bugs me. Very very important things get buried under UI decisions or app updates, and that can cost you. But with a couple of proactive habits—secure 2FA, clean browser profile, up-to-date app, and physical backups—you’ll reduce friction and sleep better on trade nights. The closing bit? Don’t treat exchange accounts like just another app; treat them like a bank vault with a mobile key. You’ll be glad you did.
FAQ
What if I don’t receive my 2FA code?
Check your phone’s network, spam folders, and message filters. Try the authenticator app if you have one, or use a hardware key. If nothing works, start the recovery flow early and have your ID ready—support queues can be long when markets move.
Is SMS 2FA safe enough?
SMS is better than nothing, but it’s vulnerable to SIM swapping. If possible use an authenticator app or a hardware key for stronger protection. Also secure your carrier account with a PIN and alerts.
How do I recognize a phishing attempt?
Look for odd sender addresses, misspellings, and urgent language. Hover over links (or better yet, don’t click and log in from your bookmark). If an email asks for your password or seed phrase, it’s a scam—never share those.
Why Transaction Simulation and Portfolio Tracking Are the Wallet Features You Actually Need
April 21, 2025 in हिन्दी-उर्दू कविता
Okay, so check this out—I’ve been fiddling with wallets for years. My instinct said that most of the UX improvements felt cosmetic, like fresh paint on an old house. Whoa! Some wallets are shiny but they still let users sign blind. Hmm… that bugs me. Initially I thought smart contract wallets would fix a lot of mistakes, but then I realized that without robust transaction simulation and clear portfolio tracking, people still get burned. Actually, wait—let me rephrase that: the technical plumbing matters more than the surface-level polish. Long story short: simulation plus tracking equals fewer surprises.
Here’s the thing. Gas estimates are one thing. Simulating the entire execution path is another. Really? Yes. Simulation helps you see reverts before you push send, spot token slippage that will eat your funds, and detect contract logic that will drain permissions. Short, sharp note: it saves money. My gut told me that wallets which only show a gas number are selling users short. On one hand, a simple estimate is accessible; though actually, it often lulls people into a false sense of safety. On the other hand, a deep simulation is more technical but it can be packaged simply—if someone builds the interface right.
Transaction simulation can feel like dark magic to users. But it’s not. Picture this: you try to swap on a DEX and the wallet runs the transaction on a forked state, then shows you the outcome, logs, and any token transfers that happen behind the scenes. You get to see the before and after. You can catch hidden approvals, sandwiching risks, or arbitrary slippage. Pretty neat, right? It’s like a dress rehearsal for your on-chain interaction. Seriously?

Why simulation should be a default feature
Simulations reduce unknowns. Simple sentence. When a wallet simulates, it tells you whether the transaction will fail or succeed under current conditions, predicts the gas usage, and sometimes even shows state changes that will happen. My experience has shown that people who see the likely outcome change behavior—less desperate gas bidding, for one thing. Something felt off about the wallets that hide this away behind developer-only toggles. (oh, and by the way…) A wallet that offers simulation as a first-class citizen is empowering; it teaches users what will happen and encourages safer habits.
On-chain UX often feels binary: proceed or cancel. But transactions have nuance. They can partially succeed, emit unexpected tokens, or trigger third-party hooks. A simulation surfaces those nuances. I’m biased, but this part of wallet design should be non-negotiable. Also, simulations create an audit trail in the UI—so if you make a mistake, you can point back to a specific simulated run and say, “look, this is what I thought would happen.” That matters when reconciling lost funds or filing a support ticket.
Okay—practicalities. How do wallets perform useful simulation? They usually spin up a forked RPC state (locally or via a provider), replay the transaction with the intended gas and calldata, and capture the trace. Some platforms enrich that trace with human-friendly details: token movements by symbol and amount, approval calls flagged, and events decoded into normal language. Long, but important: if the wallet also checks mempool dynamics and typical miner behaviors, it can warn about MEV-like risks or high slippage that only show up once the transaction hits sequencers.
Portfolio tracking: more than a balance sheet
Portfolio tracking should not be a ledger-only view. Short piece. Wallets often show token balances and a chart, and stop there. But your portfolio is also a history of interactions, approvals, and ongoing positions. The important part is lifecycle visibility: which assets are in LP positions, which tokens are wrapped, which contracts hold funds under multisig control. You deserve that context. My instinct said users want this, though actually many teams don’t prioritize it.
One trick I like is combining simulation and tracking: the wallet can simulate what happens if you try to withdraw from a vault and then show how your portfolio composition changes. It can also warn if an approval you previously granted is still wide open and could be exploited, or if a token you hold has had a recent token migration requiring action. That level of integration moves the wallet from a signing tool to a financial command center.
Also—alerts. Real people live busy lives. A good wallet notifies you when a large move affects one of your assets, or when a smart contract you interact with has been upgraded. I’m not 100% sure how many users actually manage these alerts well, but when the wallet surfaces the alert at the right time, it prevents mistakes. I’m biased here, but this kind of active assistance is what separates novice-friendly from risky.
What the best wallets get right (and a few things they don’t)
Good wallets do three things well: simulate transactions, present a clear portfolio view, and make complex actions reversible or at least explainable. Short. Another quick thought: nonce management and bundled transactions are underrated features for power users. When a wallet can simulate batched actions—like multicall swaps and approvals together—it prevents state races and reduces friction. But, caveat: more power in the interface means more responsibility for the design team.
Here’s what bugs me about many wallet designs. They over-trust the user. They show raw data without guidance. They expect users to parse EVM traces themselves. And then when something goes wrong, the support channels are slow and unhelpful. Simple fixes exist—labeling approvals, surfacing simulation outputs in plain English, and allowing a safe “dry run” mode where a transaction is simulated on a fork and the user can accept or reject based on a digest. These are not rocket science. They’re product choices.
There are trade-offs. Simulation requires compute and sometimes proprietary providers. Privacy concerns arise if you send calldata to a remote simulator. Some wallets solve this by offering optional local simulation (run in the extension) or encrypted telemetry. On one hand, cloud-based simulation offers speed and breadth; though actually, it can leak behavioral signals. On the other hand, local simulation preserves privacy but may be constrained by device resources. You can see the tension. My approach? Offer both pathways and be transparent about what gets shared.
How rabby wallet demonstrates a practical middle path
I’ve tested a number of wallet flows and I appreciate when a product balances power with clarity. One wallet that stands out in this space is rabby wallet. It integrates transaction previews, shows decoded calldata, and surfaces approval risks in ways that non-devs can understand. That kind of UX nudges users to safer choices without lecturing them. I’m biased, but that’s the model I’d like to see more widely adopted.
Rabby’s approach—simulate, explain, and then ask for consent—feels human-centered. Short sentence. It respects the user by giving information incrementally, rather than dumping raw traces on them or hiding everything behind “advanced settings.” If I were building a wallet, I’d borrow that ethos and push it further: more contextual education, actionable alerts, and an audit-log style history of simulations tied to real transactions.
FAQ
How accurate are simulations?
Simulations are usually accurate for the current mempool and chain state, but they can diverge if gas prices spike, if the mempool reorders transactions, or if contracts rely on off-chain oracles. In practice they catch most revert conditions and many logic errors. Still, treat them as a very good forecast, not an infallible prophecy.
Do simulations cost gas?
No—they’re read-only executions on a forked or simulated state. However, providers charge for compute. Wallets may absorb that cost or rely on paid simulation backends. There are also privacy trade-offs to sending calldata off-device.
Can simulation prevent hacks?
Not entirely. Simulations catch a subset of risky conditions like improper approvals, expected reverts, and obvious slippage. They won’t always reveal subtle economic attacks or front-running strategies that depend on mempool timing unless the simulation models those conditions. Still, simulation is an important line of defense.
Final thought—this is where web3 UX matures. Short. A wallet that combines meaningful simulation, clear portfolio tracking, and smart alerts turns a signing tool into a financial assistant. It changes behavior. It reduces regret. I’m not saying it’s a silver bullet. I’m saying it’s the next necessary step. Somethin’ about seeing the expected outcome before you press send gives you a second brain. And in crypto, that second brain is very very important.
Why the Right Futures Trading Platform Changes the Game (and How to Pick One)
March 25, 2025 in हिन्दी-उर्दू कविता
Okay, so check this out—trading software isn’t just a chart and an order entry box anymore. It’s an ecosystem: data feeds, backtesting engines, execution algorithms, and APIs that either sing together or crash in a heap. Whoa! Really? Yep. My instinct said the platform mattered mostly for speed, but then I dug deeper and saw how workflow, reliability, and automation maturity actually define edge. Initially I thought faster = better, but then I realized resilience and clarity win more often than raw latency in a retail setup.
Here’s what bugs me about a lot of platform reviews: they focus on shiny metrics and ignore the daily grind. Traders wake up, check margins, tweak algo thresholds, and sometimes watch screens for hours—so ergonomics matter. Hmm… somethin’ about a cramped UI or an opaque execution log can make a strategy that looked great in backtest unusable in live. Seriously? Yes. On one hand, a platform might boast sub-millisecond order routing; on the other hand, poor order management or flaky data feeds can wipe gains just as surely.
Let’s walk through what matters in a futures trading platform if you trade actively or plan to automate: market data fidelity, order routing transparency, backtest-to-live fidelity, extensibility, and support for risk controls. Short list first: data, execution, automation. Longer thought—these three interact nonlinearly; improve one and you may expose bottlenecks in another, which is why picking a platform is more like tuning a race car than buying a tool.

Market Data: the quiet backbone
Data latency and integrity are more subtle than most sellers admit. A missing tick here, a misaligned bar there—those are the little gremlins that create slippage surprises. Wow! You might not notice until you run high-frequency strategies or try to reconcile your P&L at month-end. Medium-term traders also suffer: mispriced historical bars lead to misleading drawdowns and curve-fit parameters. Actually, wait—let me rephrase that: it’s not just missing ticks; it’s how the platform normalizes, aggregates, and timestamps data that matters for reproducible results.
Practical checks: can you access raw tick data? Does the platform let you replay historical market conditions with accurate spreads and fees baked in? If you want to automate, can you simulate latency and order queuing? Those features turn backtesting from a classroom exercise into a plausible live-preview. I’m biased toward platforms that make it explicit how they treat data, not those that hide it behind “proprietary consolidation.” Oh, and by the way—always check timezone handling. It’s boring but costly.
Execution and Order Management: where strategy meets reality
Execution transparency is crucial. If your fill algorithms are a black box you can’t debug, your strategy becomes a bet on vendor reliability. Hmm… that bugs me. You want logs. You want sequence numbers. You want the ability to replay the exact order lifecycle from placement to fill or rejection. Longer explanation: firms that provide per-order diagnostics and let you script custom order types reduce time-to-fix when weird market events show up.
Here’s a checklist I share with colleagues: slippage modeling, native bracket orders, conditional OCO logic, and a clean API for manual overrides. On one hand, pre-built smart routing helps; on the other hand, you must be able to force direct market access when needed. Balancing convenience and control is a common tension—though actually, I prefer platforms that let you choose both.
Automation and Strategy Development
Automation is the big lure. Wow! The promise: build once, trade forever. Reality: strategies need observability. If your algo can’t emit metrics or trace decision points, debugging is a nightmare. My instinct said “set-and-forget,” but that’s naive. Automated live trading requires telemetry: per-trade latency, decision timestamps, confidence scores, and health checks.
Frameworks matter too. Do you code in C#, Python, or a proprietary scripting language? Each has its tradeoffs. C# often gives speed and a mature ecosystem. Python offers rapid prototyping and lots of libraries. Proprietary languages sometimes mean faster ramp for non-programmers, though they can lock you in. On the practical side, support for versioning strategies and backtest comparison tools is a huge time saver. Seriously? Yes—if you ever try to reconcile why a strategy diverged from backtest during a live session, you’ll appreciate those tools.
Risk Controls, Compliance, and Reliability
Risk features are not glamorous, but they keep you in business. Pre-trade checks, session-level limits, automated kill-switches—these are essential. A platform that treats risk as an afterthought is a red flag. Initially I thought sophisticated traders would build their own risk checks externally, but actually it’s far easier and safer to have baked-in low-latency checks inside the platform that block orders before they hit the exchange.
Reliability: uptime isn’t just a stat. It’s a behavior pattern across weekends, patch days, and volatile events. Look for published SLAs, patch notes, and community reports. Also check how the vendor handles failover and order state recovery; somethin’ like a mid-session restart shouldn’t orphan orders.
Choosing: a pragmatic approach
Start with your strategy profile. Short-term scalpers have a different wishlist than systematic swing traders. Map needs to features: if you need ultra-low latency and direct market access, prioritize a provider with colocated servers and explicit routing. If you’re heavy on strategy research and need flexible backtesting, favor platforms with robust historical tick support and scripting ecosystems.
Try to run a candidate platform in a sandbox against a paper account for several market conditions—quiet, news, and gap opens. Spend at least a few weeks. You’ll uncover quirks. And when you do your trial, embed observability from day one: logging, metrics, and reconciliation routines. I can’t stress that enough.
One practical tip: if you’re evaluating NinjaTrader, the vendor offers a full-featured trial and strong community resources. For an easy start, visit the link where you can get the installer and walkthrough: ninjatrader download. That download page is what many US retail futures traders use when they want to test locally; it’s not the only option, but it’s a solid starting point.
FAQ
Which platform is “best” for automated futures trading?
There isn’t a single winner—best depends on your latency tolerance, coding language preference, and budget. Look for platforms with transparent data handling, a strong debugging toolset, and reliable order management. Also consider community and third-party integrations, because plugins and marketplace indicators can accelerate development.
How should I validate a strategy before going live?
Use multi-year tick data, simulate fees and slippage, run walk-forward or out-of-sample tests, and rehearse live in a paper account across different volatility regimes. Add monitoring and alerts so you catch behavioral drift early. And keep a log—manual notes help spot contextual issues during live events.
Is low latency always worth the cost?
Not always. For many retail and systematic traders, predictable execution and good tooling beat marginal latency gains. Low latency is critical for scalpers and market makers, but for trend or mean-reversion strategies on daily bars, robustness and reproducibility drive returns more than shaving microseconds.
Test Post for WordPress
February 27, 2025 in हिन्दी-उर्दू कविता
This is a sample post created to test the basic formatting features of the WordPress CMS.
Subheading Level 2
You can use bold text, italic text, and combine both styles.
- Bullet list item #1
- Item with bold emphasis
- And a link: official WordPress site
- Step one
- Step two
- Step three
This content is only for demonstration purposes. Feel free to edit or delete it.
Phantom, NFTs, and DeFi: A Practical Guide to Using a Solana Browser Wallet
February 23, 2025 in हिन्दी-उर्दू कविता
Okay, so check this out—if you’re playing around in Solana’s ecosystem, Phantom is one of those wallets that quickly becomes part of your daily toolkit. Wow. It handles NFTs, token swaps, staking, and connecting to dapps without feeling like an engineering exam. My instinct said it would be smooth, and for the most part it is, though there are a few rough edges that bug me.
First impressions matter. Phantom’s interface is clean. It hides a lot of complexity behind simple buttons, which is both good and sometimes frustrating—because you don’t always see what’s happening under the hood. Initially I thought it was just another extension, but then I realized how much it ties into Solana-specific flows (fast finality, low fees, SPL token quirks). Actually, wait—let me rephrase that: it’s built for speed, and that speed changes how you think about transactions and confirmations compared with Ethereum wallets.
What Phantom does well (and where to be careful)
Phantom is great for NFT collectors. Seriously? Yes. It renders on-chain NFTs, shows metadata, and makes transfers straightforward. Medium-sized collections show up cleanly. But watch out: some NFTs rely on off-chain metadata, so the wallet’s preview might not always match the marketplace view. On one hand that’s fine—though actually, it’s worth double-checking on the marketplace before clicking “send.”
For DeFi, Phantom integrates swaps and token approvals nicely. Transactions are fast and cheap, so experimenting with small trades is reasonable. My gut feeling is to start small. Something felt off the first time I approved a token for the wrong amount—so always inspect approvals. Use the “settings” and “approvals” sections to revoke permissions you no longer need. It’ll save you headaches later.
Phantom supports hardware wallets (Ledger), which is huge. If you’re moving meaningful value or holding rare NFTs, use a Ledger. It adds a step, sure, but that security tradeoff is worth it. I’m biased, but for real assets, do not keep everything in a hot extension without some cold backup.
Installing and verifying the extension
Install Phantom only from trusted sources. I know, that’s obvious, but phishing extensions are a real problem. If you want to check a download link that someone sent, compare it to the official domain (phantom.app) and the Chrome or Edge Web Store listing. Also, you can view the extension’s permissions before adding it—don’t skip that. One place people sometimes land is a third-party page offering downloads; be cautious and verify. Here’s a link you can review: https://sites.google.com/cryptowalletextensionus.com/phantomwalletdownloadextension/ (but honestly, double-check the URL you use and prefer official channels).
When setting up, you’ll be prompted to create a new wallet or restore one from a seed phrase. Do not, ever, type your seed phrase into a website or send it to someone. Keep it offline. Write it down. Store copies in secure places. My experience: a paper backup in a safe plus a sealed secondary copy stored elsewhere works well. Oh, and hardware backups are better.
Everyday workflows: sending, receiving, staking, and NFTs
Sending and receiving SOL or SPL tokens is intuitive. Click “Send,” paste the address, and confirm. Short transactions, fast confirmations—this is Solana at work. But here’s the thing: small mistakes still cost money. Copy-paste addresses and confirm the first few characters visually. If you see a memo field or unusual prompt, pause.
NFT transfers are similar. When you transfer, Phantom shows the token’s name and collection info. Pause and confirm that’s the right item. If you plan to list or buy on a marketplace, connect Phantom and only approve the exact actions you intend. That approval flow can be subtle: sometimes sites ask for blanket permissions. Decline blanket approvals when you can.
Staking SOL in Phantom is straightforward. You can delegate to a validator from within the app. Look up validators (reputation, commission, performance) before delegating. On one hand, staking feels low-risk; on the other, validator selection matters for long-term yields and network health.
Security tips (practical, not preachy)
Be paranoid in small doses. Use a hardware wallet for big balances. Keep software updated. Only connect to dapps you trust. Revoke approvals when a dapp is no longer used. And if something smells phishy—links in Discord DMs, random airdrop prompts, urgent “verify your wallet” messages—stop. Seriously, stop. Scam social engineering is the low-hanging fruit for attackers.
Also: consider separating funds. Keep a “spend” account for daily swaps and mints, and a “hold” account—ideally with hardware wallet—for long-term assets. It sounds tedious. But it’s saved me from silly losses before.
FAQ
Is Phantom safe?
Phantom is generally considered safe as a software wallet. But security depends on your hygiene: use official downloads, keep seed phrases offline, and use a hardware wallet for significant holdings.
Can Phantom hold NFTs?
Yes. Phantom displays on-chain NFTs and lets you transfer them. It handles SPL standard NFTs and makes collection browsing straightforward. Always confirm metadata and token IDs when transferring.
Does Phantom support DeFi on Solana?
Yes. You can swap tokens, add liquidity on supported platforms, and connect to DeFi dapps. Because Solana transactions are fast and cheap, experimenting is less painful—but still, start small and check approvals.
How do I recover my wallet?
Use your seed phrase or Ledger to restore. Never share the phrase. If you lose it and don’t have a hardware key, recovery is unlikely—so back up your phrase securely.
Alright—final thought: Phantom makes Solana approachable, but the ecosystem moves fast and sometimes unpredictably. Keep learning, stay cautious, and treat your wallet like the key to your front door. You wouldn’t hand that key to strangers, right? I’m not 100% sure about everything here, but these practices have saved me from scrapes more than once. Somethin’ to keep in mind.
Test Post for WordPress
February 19, 2025 in हिन्दी-उर्दू कविता
This is a sample post created to test the basic formatting features of the WordPress CMS.
Subheading Level 2
You can use bold text, italic text, and combine both styles.
- Bullet list item #1
- Item with bold emphasis
- And a link: official WordPress site
- Step one
- Step two
- Step three
This content is only for demonstration purposes. Feel free to edit or delete it.
Why Your Mobile Wallet Should Do More Than Hold Coins — Privacy, Swaps, and Real Usability
February 12, 2025 in हिन्दी-उर्दू कविता
Whoa!
I remember the first time I used a mobile XMR wallet and felt like I had discovered somethin’ private amid a noisy market.
It was small and clumsy at first, but the instinctual relief of holding Monero on a phone — untethered from large exchanges — was immediate and oddly comforting.
At first I thought mobile wallets were just convenience tools, but then I realized they can reshape how privacy-conscious people move value without leaking metadata.
That shift in thinking matters because the choices we make about wallets ripple into everyday privacy, and sometimes into legal gray areas that most folks don’t even see coming.
Really?
A wallet should be more than a balance screen.
It should be a trust-minimized hub that lets you swap, shield, and control your coins without creating a paper trail you can’t live with later.
On one hand, custodial apps feel easy and get you trading fast; on the other hand, those conveniences come with trade-offs that are not worth it for privacy-sensitive users who value anonymity.
My take is simple: give people tools that default to privacy, but still play nice when they need liquidity or multi-currency support — and do it in a way that doesn’t require a law degree to understand.
Hmm…
Swapping in-wallet is a real game-changer.
It reduces round trips to exchanges and limits on-chain exposures, which is huge for Monero users especially, though actually—it’s complicated when you mix chains and protocols.
When a mobile wallet integrates exchange functionality, it needs to handle routing, rate slippage, and privacy implications, all while keeping UX friendly for someone on the subway or in a coffee shop.
That balance — between sophisticated backend mechanics and simple front-end interactions — is the quiet engineering art that’s often overlooked.
Here’s the thing.
Not all in-wallet exchanges are equal.
Some are thin wrappers over third-party services and leak too much information; others try to be hybrid, using relays, OTC-style liquidity pools, or cross-chain atomic mechanisms that protect metadata better.
I prefer approaches that minimize KYC touchpoints and avoid persistent user profiling, though I’m not 100% sure any solution is perfect right now.
Still, it’s better to pick a wallet with options and transparency than one that hides the plumbing under flashy buttons.
Whoa!
When testing mobile XMR wallets I looked for three core things.
One: how the wallet constructs and broadcasts transactions — does it route through a remote node, or let you run your own?
Two: whether the swap function uses trustless or semi-trusted liquidity, because that determines how much of your identity you expose when converting BTC to XMR or vice versa.
Three: how well the wallet isolates keys and handles backups, since losing your seed while swapping is very very important to avoid.

Designing for Privacy Without Sacrificing Usability
Seriously?
People often expect perfect privacy right out of the box.
But privacy is a layered practice, not a single feature you toggle on.
Initially I thought a single-button “Private Mode” would do it, but that was naive; actual privacy workflows require choices, defaults, and education built into the UX.
So wallets should guide users gently — not lecture them — while keeping advanced controls available for power users.
Whoa!
A good mobile wallet will offer options like remote-node selection, Tor or VPN routing, and in-wallet exchange routing transparency.
Those are not mere checkboxes; they materially change how much information leaks during swaps and broadcasts.
On the technical side, Monero’s privacy model differs from Bitcoin’s and that difference complicates cross-chain swaps — you need intermediaries or off-chain settlement layers that respect privacy, or else something leaks.
That said, new relay and aggregator models are emerging which reduce leakage by obfuscating timing and routing data, though they add complexity that wallets have to hide from users without hiding the truth.
Hmm…
I tried using a wallet that routed swaps through multiple relays and it felt smoother than I expected.
But there were moments when rates lagged, and the app threw up a terse error that made me pause — human error and edge cases still pop up.
Frankly, this part bugs me: good error messages are underrated, and privacy wallets often give you nothing but cryptic codes when things go sideways.
UX isn’t just pretty icons; it’s how you handle the mess.
Here’s the thing.
Backup and recovery matter as much as privacy features.
If you can trade privately but lose your seed or your backup phrase is compromised, all the privacy engineering is moot.
So whenever I’m evaluating a wallet I look at the backup options: are seeds stored on device only, is there support for mnemonic passphrases, and can I export an encrypted backup to my own cloud safely?
Those are practical trade-offs that real people will wrestle with at 2 a.m., sometimes on a bus, so the processes must be clear, fast, and forgiving.
Exchange Mechanics: Custodial vs. Non-Custodial in Wallets
Really?
There’s a spectrum, not a binary.
Custodial swaps are fast and smooth, but your privacy is surrendered in subtle ways because you’re trusting a provider with both funds and data.
Non-custodial swaps preserve control but introduce UX and liquidity challenges, often requiring routing through decentralized liquidity pools or atomic-swap protocols that are still maturing.
On the balance sheet, for privacy-first users I lean toward well-implemented non-custodial or hybrid models that minimize long-lived custody and KYC exposure.
Whoa!
Consider routing: some wallets batch or delay swap broadcasts to obscure timing correlations, and others use intermediate addresses to break linkability.
These techniques can be effective, though they increase complexity and sometimes cost.
There’s also the practical matter of fees: cross-chain swaps will inevitably layer fees and spread, and you should know when the convenience is worth the premium.
I tell people to treat swaps like travel: cheaper routes exist, but the quickest, low-exposure paths may cost more — choose based on threat model.
Hmm…
Security models are also a factor — does the wallet isolate swap keys from main private keys, and are there multi-sig options for added safety?
I experimented with a mobile wallet that supported hardware key integration and it felt bulletproof, though slightly less convenient.
It’s a trade-off I’m willing to make for larger amounts.
For everyday small transfers, a well-audited mobile-only flow is often fine, but always segment funds by purpose: spend, save, and trade buckets — and treat them differently.
Here’s the thing.
If you care about privacy and hold multiple currencies, you want a wallet that embraces both Monero’s privacy primitives and mainstream currencies like Bitcoin, without forcing you into central KYC.
That means clear disclosures about what data a swap partner collects, how long they retain it, and whether they share it with third parties.
Transparency matters more than marketing claims, because you’re trusting a tool with the map to your financial truths.
Whoa!
If you’re curious about practical options, a lot of the newer mobile wallets are striving for this balance — they document trade routes, support Tor, and let you run a node if you’re paranoid.
One place to start poking around is the project pages and web interfaces where devs post technical notes and privacy papers; sometimes the best info is buried in release notes.
I keep an eye on projects that publish both usability tests and privacy audits, and I usually try them on an old phone first to avoid risking main funds.
Oh, and by the way, if you want to check a wallet that focuses on mobile privacy and has in-wallet features, see this link: https://cake-wallet-web.at/ — their docs are straightforward and their approach is worth reading.
FAQ
Can a mobile wallet truly protect my privacy?
Short answer: mostly, if used correctly.
Longer answer: mobile wallets can protect metadata and obfuscate on-chain links, but you must configure node access, routing (Tor/VPN), and swap providers carefully.
Also, habits matter — address reuse, screenshots, and cloud backups can leak data even when the wallet is sound.
Are in-wallet swaps safe for Monero?
They can be, depending on the swap architecture.
Non-custodial atomic or decentralized routing preserves more privacy, while custodial swaps may require KYC that undermines anonymity.
Check whether the wallet publishes how swaps are routed and whether it partners with privacy-respecting liquidity providers.
How do I start testing without risking my funds?
Use small amounts first.
Try on a secondary phone or a sandbox profile, and test backup and recovery procedures before moving big balances.
Work incrementally: test node settings, then swap flows, then hardware integrations — each step reduces surprises later.
Why I Trust Monero Wallets — and Why You Should Care About XMR Storage
February 6, 2025 in हिन्दी-उर्दू कविता
Whoa!
I’ve been poking around privacy crypto for years, and Monero still feels refreshingly stubborn. My instinct said this was the one to stick with early on. Initially I thought privacy coins would fade, but then I watched adoption and tooling quietly improve — and that changed my view. There are trade-offs, of course, though actually, wait—let me rephrase that: trade-offs mostly favor users who care about on-chain privacy, but those users need a plan.
Seriously?
If you’re reading this, you probably want to hold XMR securely and privately. You’re not alone; people in coffee shops and on airplane rides here in the US ask me about wallets all the time. On one hand hardware wallets are a no-brainer for long-term storage, though on the other hand usability matters a lot for day-to-day spending. My advice fluctuates depending on needs — offline cold storage for savings, a small mobile wallet for daily use, and a clear backup strategy in between.
Hmm…
Hardware wallets give peace of mind. Medium-length sentences help explain why: they isolate private keys from networked devices. Long complex thoughts matter here because the real risk is not just theft, but seed leakage over time through sloppy backups or reused systems which can cascade into permanent losses if you’re not careful. In practice that means using official firmware, verifying device authenticity, and keeping your seed phrase under multiple layers of physical security.
Here’s the thing.
Using remote nodes reduces local resource needs, but it leaks metadata unless you trust the node. Many users default to remote nodes because running a full node is annoying — I get that; been there, done that, left clothes on the line. Still, running your own node is the most privacy-preserving option, and even running a pruned node helps a lot. There’s a middle path: run a private node on a cheap VPS and connect your wallet to it, though that requires comfort with server setup and an eye on costs (and trust boundaries).

Practical steps and a place to start
If you want a place to start that isn’t spammy, check the xmr wallet official site for basic downloads and instructions. I’m biased, but having one canonical page to verify builds and get links from is handy. On a tactical level: split your holdings, use a hardware wallet for the bulk, keep a hot wallet for daily small spends, and rehearse a recovery. Also, write your seed on metal or at least somewhere that can survive a leak or a flood — paper is fine temporarily, but it’s fragile.
Whoa!
Here’s a few practices I follow. First, air-gapped signing for large transfers when possible. Second, seed backups in multiple geographically separated locations. Third, periodic checks: make sure you can recover, because a seed that looks fine on paper might fade or smudge. I’ll be honest, this part bugs me — too many people assume a photo of a seed phrase is a backup. It isn’t. Photos leak, devices get hacked, and cloud storage is the enemy of privacy.
Seriously?
When selecting wallet software pay attention to provenance and community reviews. Open source matters because it allows independent audits, though open source alone isn’t a silver bullet; build reproducibility and active maintainers matter too. Initially I trusted a UI because it looked slick, but then I realized that ease of use can hide risk — so vet dev channels and check release signatures. On top of that, keep your system patched and avoid wallet use on compromised devices.
Hmm…
For many US users the friction is legal and practical. Banks, exchanges, and tax forms create behavioral pressure that pushes people toward custodial services, which is the opposite of privacy. My instinct said use hardware then move on, but the reality is more complicated — people need habits that fit their lives. So plan for compliance where required, but minimize exposure where you can: withdraw to cold storage, and don’t keep large balances on exchanges.
Here’s the thing.
Community support is underrated. Join local or online groups, but be cautious about oversharing. Talk in generalities when you need help; don’t post your address or balances. On one hand there’s value in quick tips, though on the other hand privacy slips fast when folks brag about holdings. Practice humility; privacy is a process, not a feature you toggle on once and forget.
FAQ
What’s the safest way to store XMR?
Split holdings. Use a hardware wallet for the bulk of your XMR, a mobile or desktop wallet for small day-to-day amounts, and a tested recovery plan. Offline cold storage on trusted devices plus a verified seed backup on metal is my go-to. Also, periodically test the recovery on a fresh device to be sure the seed works.
Should I run my own Monero node?
Yes if you can. Running your own node offers the best privacy and sovereignty. If that’s too heavy, consider a trusted VPS or use privacy-respecting remote nodes cautiously. Remember: remote nodes trade convenience for some metadata exposure.
How do I choose a wallet?
Look for active maintainers, reproducible builds, and community trust. Consider hardware compatibility, ease of use, and whether you can connect to your own node. I’m not 100% strict on one approach — different people need different setups — but verify builds and keep your software updated.
Test Post for WordPress
February 4, 2025 in हिन्दी-उर्दू कविता
This is a sample post created to test the basic formatting features of the WordPress CMS.
Subheading Level 2
You can use bold text, italic text, and combine both styles.
- Bullet list item #1
- Item with bold emphasis
- And a link: official WordPress site
- Step one
- Step two
- Step three
This content is only for demonstration purposes. Feel free to edit or delete it.
Why I Trust (and Worry About) Mobile Privacy Wallets — A Close Look at Cake Wallet for Monero and Bitcoin
January 31, 2025 in हिन्दी-उर्दू कविता
Whoa! Okay, so here’s the thing. Mobile crypto wallets are convenient in a way that almost feels reckless sometimes. They live in your pocket, sync on cellular, and let you move serious money while waiting in line for a sandwich. My instinct said: this is brilliant. Then I dug in and felt a little queasy… because convenience and privacy rarely ride together without compromise.
I use mobile wallets a lot. Not for everything, but for a practical slice of daily crypto life — testnets, small trades, and quick Monero sends when I need stealth. At the same time, I’m picky. I’m biased, but I prefer non-custodial designs, local seed phrases, and options to use my own node. Cake Wallet comes up a lot in conversations. It’s easy to recommend casually, though actually, wait—let me rephrase that: I recommend it conditionally. You should know why, and you should know the pitfalls.
![]()
So what does Cake Wallet get right?
First off, Cake Wallet understands the basics that matter to privacy people: non-custodial keys, seed backups, and support for Monero (XMR). Seriously? Yes. Monero is its big draw. The wallet handles XMR’s unique mechanics — ring signatures, stealth addresses, and RingCT — so you can send truly private transactions without dealing with a full node if you don’t want to.
That’s huge. For many users, running a full Monero node on a phone is impractical. Cake gives a lighter-weight path. On top of that, it usually offers a straightforward UI for BTC and some other coins, meaning you can keep multiple balances in one place. That convenience is very very nice. But again, convenience invites trade-offs.
Initially I thought Cake Wallet was simply another mobile app. Then I realized how much subtle design matters: where the remote node is hosted, how the wallet handles transaction broadcasting, and whether metadata leaks are minimized. On one hand the app reduces friction. On the other hand you may be handing off some privacy to remote infrastructure. Hmm…
Pro tip: if you’re curious about downloading it right now, check this link — https://sites.google.com/mywalletcryptous.com/cake-wallet-download/ — but verify the source before you tap install, ok? I’m not 100% sure the site will always be maintained, so double-check the app publisher and reviews in your app store.
Common privacy trade-offs to watch for
Short version: remote nodes, analytics, and OS-level telemetry are the top three culprits. Remote nodes are convenient because they let your wallet read the blockchain without downloading it. But those nodes can see your IP and the history of addresses you query. It’s a subtle leak that many people ignore until it’s too late.
On modern phones, apps often phone home. Some of that is benign — update checks, crash reports. Some of it is not. Cake Wallet has historically tried to keep things lean, but app ecosystems change. So keep an eye out. If something feels off, uninstall, clear the app data, and re-seed from your mnemonic on a fresh install.
Also: backups. Write down your seed. Physically. Do not screenshot it and stash the screenshot in cloud storage. That advice is boring but very very important. I say this as someone who once almost lost access because I trusted my phone too much.
Practical setup for better privacy
Start on a clean device when you can. Seriously. A phone with fewer installed apps has fewer attack vectors. Disable unnecessary permissions. Use a VPN or Tor when connecting to a remote node, though be mindful that Tor can sometimes break connectivity for light wallets. If you can run your own node at home and connect to it over a secure channel, do that. It’s the gold standard.
On the wallet itself, choose strong PINs and enable any available biometric fallback only if you understand the trade-offs. Biometrics are great for daily convenience, but they can complicate legal and forensic scenarios. I’m not 100% sure people want that nuance, so I’m putting it plainly: think about future-you, not just now-you.
Finally, keep the app updated. Updates fix security bugs. They also sometimes add telemetry. Read the changelog if it’s available. If an update suddenly asks for odd permissions, pause and investigate.
Typical failure modes — and what to do
People make small mistakes that become big problems. Example: seeding a wallet on a rooted phone because “I need this app” — bad idea. Example two: buying a used phone and restoring from a cloud backup that contains wallet data — risky. There’s also social engineering: someone asks you to export a view key “to help troubleshoot” — don’t do it without validation.
If something goes wrong: freeze activity, don’t import the seed to any third-party service, and if possible move funds to a new wallet that you set up on a clean device. Yes, that can be a pain. But losing funds or privacy is worse.
FAQ
Is Cake Wallet fully private?
It’s private by design for Monero transactions, since XMR’s protocol gives inherent privacy protections. But the overall privacy you achieve depends on choices outside the app: node selection, OS privacy, and network routing. On the balance, Cake can be a strong tool—when used carefully.
Can I use Cake Wallet for Bitcoin privacy too?
Yes, to an extent. Bitcoin lacks Monero-level privacy by default, so you need extra practices: coin control, CoinJoin services, and avoiding address reuse. Cake Wallet simplifies BTC management, but it’s not a magic privacy solution. Use it with informed habits.
What if I want absolute privacy?
No mobile setup is perfectly private. For absolute control, run your own full nodes and prefer hardware wallets and air-gapped signing when possible. That’s extreme for daily use, though, and most users will accept reasonable trade-offs.
Okay, to wrap this up — though “wrap up” sounds too neat for something messy like privacy — here’s my felt take: Cake Wallet is a useful, pragmatic tool if you value Monero and want mobile convenience. It isn’t a silver bullet. Use it smartly, and assume nothing is fully private by default. Learn a bit about nodes, backups, and network hygiene. You’ll sleep better. Or at least, you’ll sleep with fewer “oh no” moments in the morning.
Test Post for WordPress
January 23, 2025 in हिन्दी-उर्दू कविता
This is a sample post created to test the basic formatting features of the WordPress CMS.
Subheading Level 2
You can use bold text, italic text, and combine both styles.
- Bullet list item #1
- Item with bold emphasis
- And a link: official WordPress site
- Step one
- Step two
- Step three
This content is only for demonstration purposes. Feel free to edit or delete it.
Test Post for WordPress
January 17, 2025 in हिन्दी-उर्दू कविता
This is a sample post created to test the basic formatting features of the WordPress CMS.
Subheading Level 2
You can use bold text, italic text, and combine both styles.
- Bullet list item #1
- Item with bold emphasis
- And a link: official WordPress site
- Step one
- Step two
- Step three
This content is only for demonstration purposes. Feel free to edit or delete it.
Why Yield Farming and Staking Pools Aren’t Opposites — They’re Competing Tradeoffs
January 6, 2025 in हिन्दी-उर्दू कविता
Whoa! This whole space moves fast. Seriously? One week a protocol feels bulletproof; the next it’s a cautionary tale. My instinct said years ago that liquid staking would change how people chase yield, and, well, something felt off about how folks simplified the tradeoffs. I’m not claiming to have all the answers. Actually, wait—let me rephrase that: based on analysis of on-chain flows, protocol economics, and community governance trends, it’s clear there are layers here that most short takes miss. Here’s the thing. You can chase high APRs today and still get roasted by systemic risks tomorrow.
Okay, so check this out—yield farming, DeFi protocols, and staking pools all promise yield. But they promise it in different currencies of risk. Yield farming commonly pays in native tokens plus fees. Staking pays in base protocol rewards (like ETH issuance) and sometimes fee shares. Each reward stream behaves differently under stress. At a glance that seems obvious. On the other hand, though actually, the devil is in the composition of counterparty and smart-contract risk, liquidity, and composability.
Let me be direct: yield is not just about percentage points. It’s about timing, liquidity, and how the protocol captures revenue. For example, a DeFi pool might offer 50% APR by minting governance tokens and inflating supply. Looks sexy. But inflation dilutes long-term holders, and the farming contract could be a single-point-of-failure. Here’s what bugs me about headlines that only quote APYs—they treat the future like a stable rate. It isn’t.
First principle: understand where yield actually comes from. Fees, token emissions, underlying staking rewards, and ancillary strategies (like MEV capture or rebalancing) are typical sources. On-chain, you can trace these flows. But each source has a fragility. Fees disappear under low usage. Emissions end or get rebalanced. Staking rewards hinge on validator performance and consensus rules. Hmm… there are no free lunches—only tradeoffs.

Liquid Staking vs. Yield Farming: Complementary, Not Mutually Exclusive
Liquid staking introduced an elegant abstraction: unlock staked capital liquidity without exiting the consensus layer. People often point at Lido as the poster child of this approach. If you want to read more about one major liquid staking option, see the lido official site. That said, liquid staking tokens (LSTs) like stETH, rETH, or similar are not magic. They trade, they peg (imperfectly), and they create new vectors for DeFi composability.
Initially I thought LSTs would simply replace risky farms. But then realized the opposite: LSTs became a base asset for more exotic yield strategies—so farming on top of staking became a thing. On one hand, composability multiplies opportunity. On the other, it multiplies systemic coupling: if an LST depegs, leveraged positions and LPs can unwind in ugly ways. I’m biased, but stacking LSTs in high-leverage pools makes my stomach churn. Somethin’ about that concentrated risk feels like a classic leverage trap.
Consider three scenarios. One: you stake ETH directly as a diversified holder, gaining issuance and helping decentralization. Two: you stake via a pooled liquid-staking provider and use the LST to farm extra yield (e.g., in an AMM pool). Three: you farm in a leveraged strategy that shorts or overweights LST exposure across many protocols. Each step adds vectors: custodian/contract risk, peg risk, and liquidation spirals. You decide where to sit on that spectrum.
There’s also governance risk. Many high-yield farms rely on token incentives that central teams control. If governance votes to change emission schedules, or if a multisig signs a bad upgrade, yields can vanish fast. DeFi protocols are experimental by design. That reality is uncomfortable, and it should be.
Practical Framework for Evaluating Yield Opportunities
Here’s a simple mental checklist I use when evaluating any yield strategy. It’s not exhaustive. But it’s pragmatic.
- Source of yield: fees, issuance, emissions, or service revenue?
- Duration risk: is the yield time-limited (token emissions) or ongoing (protocol fees)?
- Counterparty surface: single multisig, decentralized set of smart contracts, or external oracles?
- Liquidity & exit path: can you get out during stress, or is the position dependent on peg stability?
- Composability chain: how many protocols link together to produce that APR?
- Governance & upgradeability: are there admins who can change rules instantly?
Answering these reduces mental overhead. For instance, a pool with high fees but low TVL that pays via fees tends to be more sustainable than one where most of APR comes from token emissions and a small team controls the minting. This is very very important if you plan to hold long-term positions. Also, consider practical limits: slashing risk for Ethereum staking is low vs. other chains, but it’s not zero. Validator misconfiguration, client-level bugs, and social coordination failures have precedent.
On MEV capture: sophisticated staking operators now run MEV-boost relays to capture extra yield for validators. That yield can be meaningful. But remember—MEV revenue distribution can be opaque, and validator operators differ in transparency. A provider claiming “maximized MEV” might concentrate power, which creates longer-term centralization tradeoffs. On one hand you get yield. On the other hand you consolidate influence over block production and proposer choice. Tradeoffs.
Taxes matter too. Staking rewards, token emissions, and realized gains from LPs are treated differently by tax authorities (and often treated inconsistently by people). I’m not a tax advisor. But you should absolutely consider the taxable nature of yield when calculating net returns. This part bugs me because it often gets ignored until late—then it’s painful.
Concrete Strategy Ideas — With Guardrails
Okay, practical guidance. Not investment advice. But useful rules of thumb.
1) Core-and-barbell: keep a core of unlevered staking exposure (either self-staked or through a reputable pooled provider) representing your long-term conviction. Use a smaller “barbell” for experimental yield farms. This reduces tail-risk concentration. I like this because it limits blow-up potential while letting you explore new alpha.
2) Prefer fee-based yields for long holds. Fee capture aligns incentives with protocol usage. Emissions are temporary. Think of fees as rent and emissions as moving van promotions. Initially I favored emissions-heavy farms for quick gains, but that approach aged poorly in several cycles.
3) Understand peg risk for LSTs before using them as collateral. If a protocol mints an LST with a complex rebasing mechanism, stress-test the scenarios where withdrawals halt. What happens to your LP token value then? I’m not 100% sure on every protocol nuance, but reading the withdrawal/exit model should be a priority.
4) Look at operator decentralization for pooled staking. How many validators? Who picks them? Are there slashing insurance mechanisms? These questions aren’t glamorous, but they matter when large stakes are concentrated. Decentralization is both a security and governance metric.
5) For short-term yield chases, set stop-losses and time-box experiments. Farming with high APRs can be addictive. Don’t let FOMO force leverage into opaque contracts. Seriously, set limits—mental or hard-coded—before you enter.
FAQ
What is the main risk of stacking yield strategies (staking + farming)?
Layered strategies compound risks. Peg/peg-break of LSTs, smart-contract bugs, liquidation cascades, and governance changes are common failure modes. If one layer fails, others can cascade. So diversification across mechanisms and time horizons helps.
Are liquid staking tokens safe enough to use as collateral?
They can be, but “safe” is relative. Evaluate the provider’s withdrawal mechanics, peg maintenance, and contract upgradeability. If the LST relies on a central contract that could be paused, that’s a conditional risk when used as collateral.
How should I compare APRs across protocols?
Don’t just compare headline APRs. Decompose the yield into its sources, model potential drawdowns under stress, and estimate realistic after-tax returns. Factor in liquidity—if the APR assumes reinvestment but you can’t exit without slippage, the math changes.
Final thought: the space rewards curiosity but punishes overconfidence. Initially I thought yield farming was the clearest path to alpha; now I see it as a toolkit that must be wielded carefully, with capital allocation, stress scenarios, and an honest appraisal of governance risk. There’s beauty in composability, and danger too. I’m intrigued, cautious, and not entirely sure where the next cycle will favor—protocols that prioritize sustainable fees or those that ride fresh token narratives. Either way, keep learning, read contracts (or have someone you trust read them), and don’t treat highest APR as the sole decision metric. Somethin’ tells me your future self will thank you.

तेरी हरयाली इन आँखों में है वरना
September 5, 2015 in शेर-ओ-शायरी
तेरी हरयाली इन आँखों में है वरना,
दिल तो कल भी रेगिस्तान था और आज भी है

मेरी मोहब्त को सलाम कर तू
September 5, 2015 in हिन्दी-उर्दू कविता
मेरी मोहब्त को सलाम कर तू
मेरी मोहब्त को सलाम कर तू ओ बेवफ़ा
तूने ज़हर देकर बेवफ़ाई निभाई
और हमने जान देकर आशिक़ी
तू चाहती थी छोड़कर जाना
तू चाहती थी छोड़कर जाना
और हम दुनिया छोड़ कर चले आये
कहती हो खुश हु आज
मेरा दिल ठुकराकर
और हम
और हम आज फिर से आंशू बहा आये
हिम्मत तो बहुत थीं
दुनिया से लड़ने की
और जीत लेते हम भी इस जहाँ को
लेकिन तेरे सामने हम खुद को हार आये
पोस्ट मार्तम कर ले यमराज
तू भी पोस्ट मार्तम कर ले यमराज
लेकिन दिल
लेकिन दिल तो हम अपना वही छोड़ आये

